Data Loss Prevention (DLP)
UK National Cyber Strategy: BAE Systems Response
The new UK National Cyber Strategy represents a key moment in cyber policy and ambitions. Here, we reflect...
The edge advantage
Reduce costs and improve performance with edge computing. Read The edge advantage, and you'll understand...

Network Security Approaches and the Case for Zero Trust
Top executives say that legacy network technical baggage is holding them back from transforming their...

The 4 Benefits of VPN Elimination
The corporate perimeter as you know it no longer exists. Virtual private network (VPN) vulnerabilities...
Essential How-To Guide: Prevent Accidental Emailing
NO ORGANIZATION IS IMMUNE TO HUMAN ERROR In this e-book you'll get a closer look at data breaches and...
Cloud Data Security 2023 Report by ESG, a division of TechTarget
…More than half (59%) of respondents believe that more than 30% of their organization's sensitive data...
Bridging the Gap of Grief with Business-Driven Security
Worldwide spending on information security products and services will reach $86.4 billion in 2017, an...
Supporting Success in Federal Government Healthcare
Automation, technology expertise, and a dedicated partnering philosophy are key to driving success. And...
Pain & Progress: Cybersecurity and Business Risk Study
Despite their best efforts and investments, some organisations still experience difficulty as a result...

Delivering Real-time Cloud Security Without Trading Off Performance
There has been a long-standing tradeoff between security and performance, and security often gets the...

An Overview of Cato Data Loss Prevention (DLP)
ata is the most valuable asset a modern enterprise has. The evolving threat landscape and shift to cloud...

Cloud Adoption and Risk Report
The recent work from home mandate has dramatically changed how we live and work. Organisations are getting...
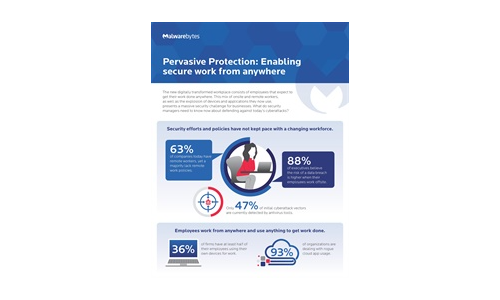
Pervasive Protection: Enabling Secure Work From Anywhere
The new digitally transformed workplace consists of employees that expect to get their work done anywhere....
Sign up for Cyber Security Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.