Endpoint Protection

Understanding Why Multi-Signal MDR Matters
MDR providers can only detect and respond to what they can see. A multi-signal approach is paramount...
5 Steps Toward Cybersecurity Resilience for Government Agencies
Cybersecurity attacks continue to grow in number, in complexity and in impact. State and local government...
Multi-Vector Protection
Educating users is an undeniably effective way to protect them from phishing and other malware, but it...
Security Operations Maturity Model
A practical guide to assessing and improving the maturity of your security operations through Threat...
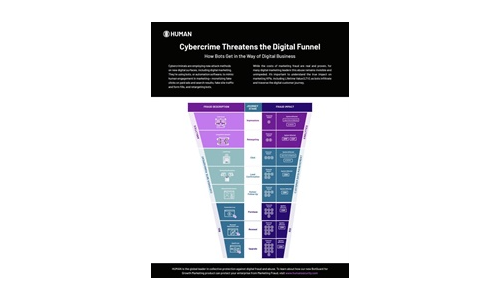
Cybercrime Threatens the Digital Funnel
Cybercriminals are employing new attack methods on new digital surfaces, including digital marketing....
Escape the Ransomware Maze
Ransomware is an ever-evolving form of malware designed to steal business-critical data and then sell...

Microsoft Digital Defense Report
Over the past year the world has borne witness to a burgeoning cybercrime economy and the rapid rise...
Six Steps to Successful and Efficient Threat Hunting
Rather than waiting for an alert, threat hunters proactively assume that an advanced adversary operates...
Using MITRE ATT&CK™ in Threat Hunting and Detection
Threat hunting is the process of proactively searching for malware or attackers that reside on your network...

The Evolution of Cybersecurity
Cybersecurity Through the Years As we look at the ever-increasing, technology-dependent cyber environment...
How to protect your business from ransomware
Read this guide to gain an insight into how you can take proactive steps to keep your company's files...

5 Benefits of Partnering with Webroot
While cyberattacks continue to evolve in volume, organization, and sophistication, security technology...
Cybersecurity Governance for Small and Medium Businesses
Building a foundation to enable cybersecurity governance is key. The cyber threat landscape is constantly...
Sign up for Cyber Security Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.


