Network Security
Farewell ISDN. Hello All-IP.
Analogue and ISDN telephony is a thing of the past – telephony today is mostly internet-based. Voice-over-IP...
The Shared Responsibility Model Explained
In a cloud environment, your service provider takes on a share of many operational burdens, including...
Remote Access Security checklist for every IT admin
Keep your remote workforce secure and productive. Find everything you need to ensure remote workforce...

5 Reasons Why Software Security is More Critical Than Ever
Vulnerable software and applications are the leading cause of security breaches. Couple this with the...

The Future of Cybersecurity For Today’s Cloud- and Mobile-First World
Today, there's a sharp focus on embracing zero trust as the future of cybersecurity. With apps, users,...
Vulnerability and Patch Management
Patching vulnerabilities is a constant battle for organizations, which is why threat actors frequently...
Edging Towards SASE: Next generation networking, cloud and security
The global pandemic has delivered a paradigm shift in the relationship between employees and their workplace....

5 Tips for Managing Third-Party Risk
Across industries and around the world, executives remain preoccupied with digital transformation. According...

Elastic Cloud Gateways: The Evolution of Secure Cloud Access
Enterprise security groups today face a daunting task. While their core responsibility of protecting...
Sophos 2022 Threat Report
Interrelated threats target an interdependent world. We believe that shifting the timescale of attack...
The edge advantage
Reduce costs and improve performance with edge computing. Read The edge advantage, and you'll understand...
What is Zero Trust? (Really)
Over the last decade, cybersecurity has been focused on the challenge of securing increasingly vulnerable...
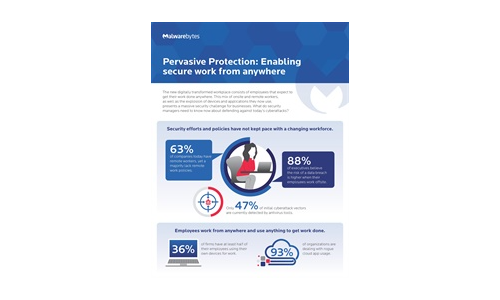
Pervasive Protection: Enabling Secure Work From Anywhere
The new digitally transformed workplace consists of employees that expect to get their work done anywhere....
Sign up for Cyber Security Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.


