Latest Whitepapers
You Got Phished, Now What?
Security leaders work hard to prevent successful phishing attacks. But, despite email security solutions...
Carbonite Endpoint Protection Myths
Myth: My endpoint data is secure because I have anti-virus software. Myth: Online storage is an effective...
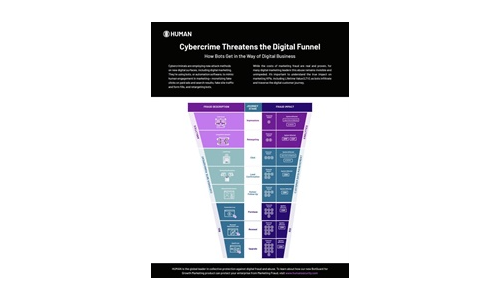
Cybercrime Threatens the Digital Funnel
Cybercriminals are employing new attack methods on new digital surfaces, including digital marketing....
Security Operations Maturity Model
A practical guide to assessing and improving the maturity of your security operations through Threat...

Lessons from REvil’s Return
Ransomware is not just another buzzword. It is a very real threat to businesses and educational institutions...
Protect K-12 Schools from Cyberattacks with Active Breach Protection
Ransomware is not just another buzzword. It is a very real threat to educational institutions of all...

Protecting your content against cyber threats and data loss
How the Content Cloud safeguards your most valuable information Your business runs on content — but...
NAIKON: Traces from a Military Cyber-Espionage Operation
NAIKON is a threat actor that has been active for more than a decade. The group focuses on high profile...

The Evolving Cybersecurity Landscape
Transformation to the cloud is no longer a choice but a business necessity. Whereas before the transition...
An Authentication Authority at Your Fingertips: PingFederate
Having an authentication authority within your infrastructure allows you to have a single source of truth...

High Security “to Go”
In the wake of digitalisation, the trend towards mobile work practices is also leading to profound changes....
Redefining Data Loss Prevention (DLP)
Data doesn't move itself. People—whether they are negligent, compromised or malicious—move data in...
2022 Cost of Insider Threats: Global Report
Independently conducted by Ponemon Institute External attackers aren't the only threats modern organisations...
Sign up for Cyber Security Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.








